The price of information breaches is predicted to rise from $3 trillion every year to greater than $5 trillion in 2024, reveals “State of Cybersecurity Resilience 2021” report. That clearly explains the necessity for corporations to have a well-grounded cybersecurity plan. Whereas that stands true with all the businesses throughout all industries, direct promoting corporations have to take additional take care of safeguarding their enterprise in the perfect curiosity of their prospects.
Direct promoting corporations retailer prodigious quantities of non-public info of shoppers, distributors, and staff. A lean safety framework can show deadly to the enterprise. At this time, 43% of cyber assaults goal small companies, particularly these within the authorized, insurance coverage, retail, monetary, and healthcare sectors. Companies face cybersecurity accidents when they’re least ready for it. So having a foolproof safety plan in place is the final word weapon to defend the attackers earlier than they even consider concentrating on you.


What’s cybersecurity?
Cybersecurity is the apply of defending belongings that corporations and people undertake to safeguard their vital methods and delicate info from digital assaults. A powerful cybersecurity structure can safeguard digital belongings and vital private and enterprise info.
Earlier than we draft a complete cybersecurity plan, let’s define the potential threats that might block the expansion of your direct gross sales enterprise.
Forms of cyber assaults that may hamper your direct promoting enterprise
In direct promoting, fairly than the monetary info, attackers give attention to the non-public and behavioral info of people both to personally profit from it or to make a fortune by promoting it to the darkish net the place this info is used for malicious causes unknown.
These cyber thugs unleash threats in a wide range of methods making it arduous for corporations and people to defend themselves.
Malware assault
In any other case known as “malicious software program” or “virus”, malware is a program constructed to mechanically run unauthorized actions on the sufferer’s system. They assault your system creating malfunction and corrupting your arduous drive or servers. It’s sometimes delivered over a community or exterior units related to your system.
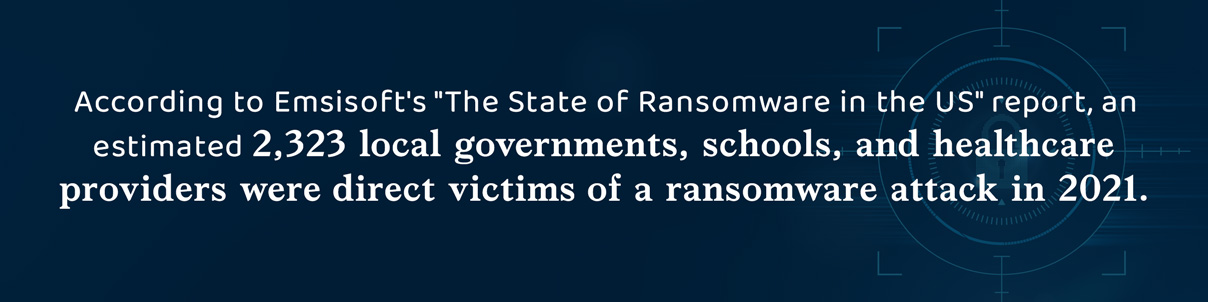
Ransomware assault
Ransomware is a type of malware that’s despatched to the goal system both by way of electronic mail or different onsite or inapplication downloads. Ransomware holds the system hostage demanding ransom from the sufferer. As soon as the quantity is paid, the attacker handovers the plan to revert the assault. These software program recordsdata exploit system vulnerabilities that the corporate or people haven’t addressed. The actual fact of the matter is that no antivirus can safeguard or detect ransomware assaults.
Phishing
Phishing assaults are sometimes finished by way of electronic mail the place the person is tricked into clicking a hyperlink that exposes your organization info comparable to private information, monetary info, and passwords to the attackers. Phishing, being the commonest kind of assault, is concerned in 36% of information breaches, in keeping with Verizon’s “2021 Knowledge Breach Investigations” report.
Phishing seems in several types sometimes called spear phishing or social engineering, whaling, and vishing. Based on PurpleSec, 98% of cybercrime depend on social engineering to perform efficiently.
Cross-site Scripting (XSS)
The attacker injects malicious scripts into web sites considered by victims. It’s supposed at gaining unauthorized entry to information, accounts, or purposes. As soon as the entry is obtained the attacker positive aspects full management and may carry out any motion the person is allowed to do on the particular web site or software.
DDoS assaults
Distributed Denial of Service assaults are focused at your web site denying customers entry to your companies. It disrupts the conventional functioning of your web site with spam site visitors flooding from a number of distant places.
The frequency of DDoS assaults rose to five.4 million within the first half of 2021 in comparison with the identical interval the earlier 12 months. Within the fourth quarter of 2021, Cloudflare reported a 175% improve within the quantity of ransom DDoS assaults in comparison with the third quarter.
Whereas these are simply the frequent sorts of assaults, these statistics present a transparent perception into the rising density of cyber assaults and the necessity to have an end-to-end safety structure in place.

Growing a direct gross sales cybersecurity technique
One research by the College of Maryland signifies that there’s a cyber try each 39 seconds. Ever imagined the variety of cyber makes an attempt your companies should be going through day by day? Now that you already know an antivirus or a PCI DSS compliance alone can’t meet your concern, try to be up for one thing extra deliberate and powerful.
A cyber assault can price corporations a terrific deal. A current research by IBM’s safety division revealed that information breaches now price on common $4 million and the fee per document breached roughly quantities to $158. It isn’t simply concerning the info being stolen however the authorized and monetary penalties that it might incur, the end result could be devastating. Cybersecurity breaches additionally assault the model belief constructed for years collectively. Each buyer and distributor belief are constructed on the way you safeguard their info and pursuits. As soon as that’s damaged that might actually be the tip of your small business.
A complete cybersecurity protection on your direct promoting enterprise
We’ve devised an 8-layered protection plan that will help you securely handle your direct promoting enterprise in opposition to challenges and threats, and safeguard your buyer pursuits.
Detect system vulnerabilities
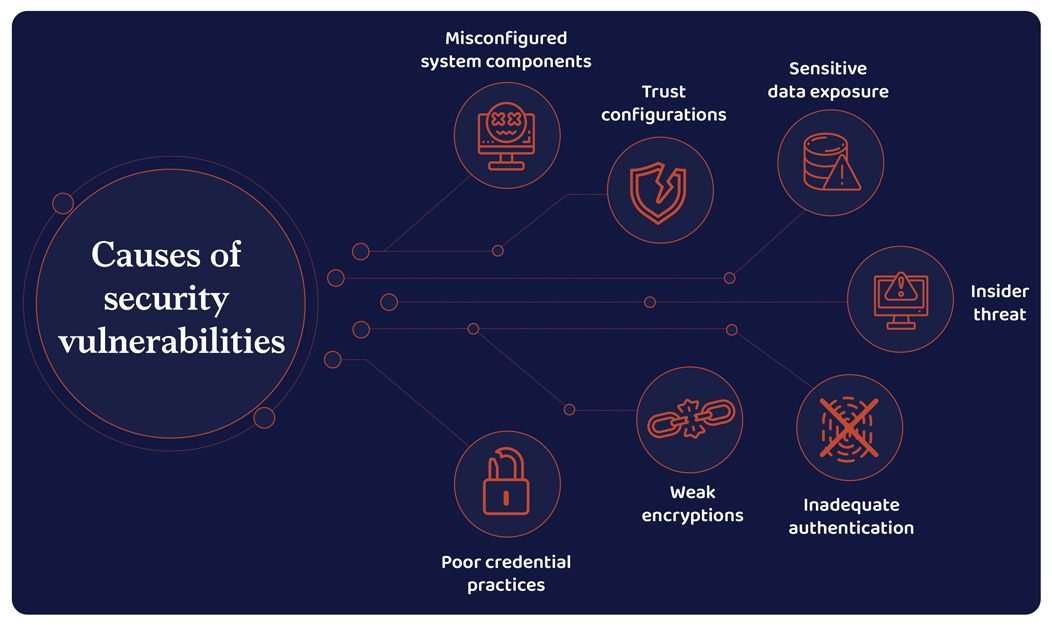
Unattended or unidentified safety vulnerabilities result in interrupted enterprise processes including to the damages prompted to buyer and distributor confidence and ultimately to the group’s fame itself. What organizations should give attention to is adopting rapid measures to restrict the harm and weak point eliminated.
In the beginning, corporations will need to have a blueprint on how vastly their information is spanned throughout the system. At all times analyze and prioritize safety dangers. Always monitor your system for vulnerabilities with penetration assessments and software program audits. Figuring out and fixing the problems on time might help mitigate the danger of being focused.
Undertake a zero-trust framework
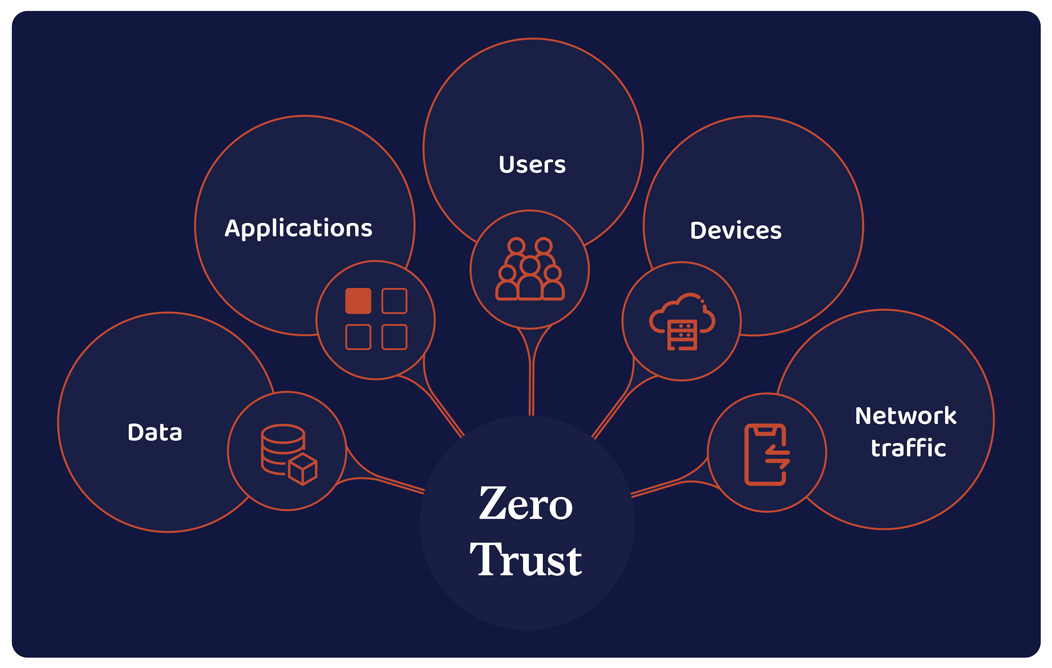
Guarantee solely the precise folks have entry to the precise sources. Safe every part from cell units to servers with authentication. In a research performed by Microsoft, The Complete Financial Impression™ of Zero Belief options, implementing a zero-security framework ensures a 50% lowered likelihood of information breach and over 50% improved safety effectivity.
Construct your zero-security structure retaining your community, endpoints, information, and person account safety ranges in thoughts. Define a strict person entry coverage to folks throughout your group.
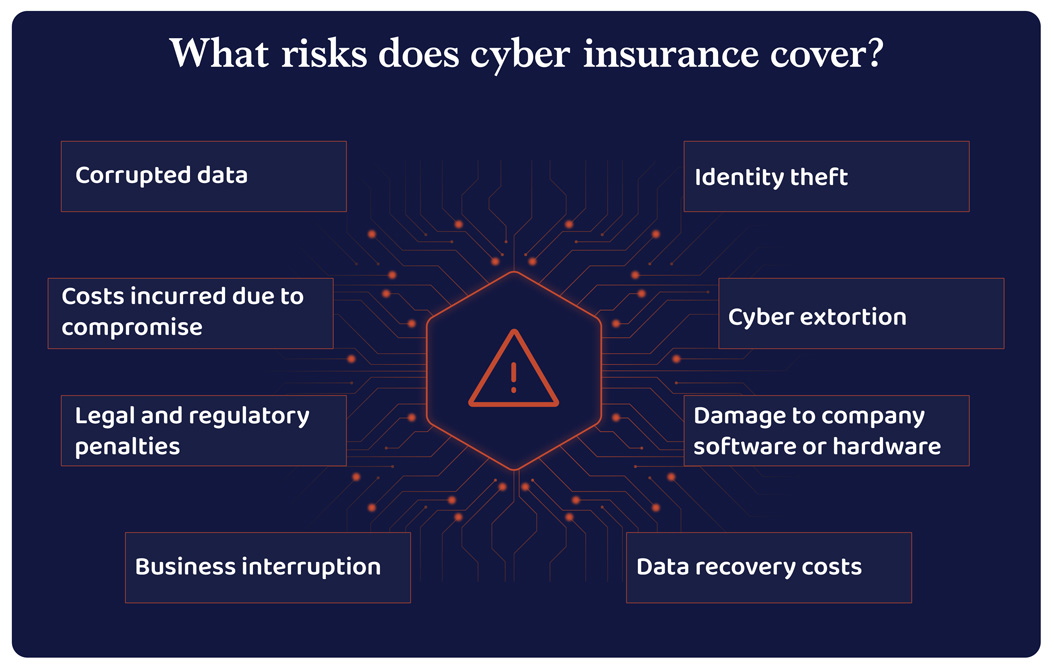
Cyber insurance coverage provides you complete protection of your small business liabilities together with person info, social safety numbers, bank card info, and well being data in opposition to information breaches. Most cyber insurance coverage insurance policies cowl information loss, cyber extortion, cost frauds, pc frauds, and lack of income attributable to breaches.
Cyber insurance coverage helps the corporate’s dedication and accountability to keep up regular compliance and regulatory normal in dealing with giant quantities of person info.
Educate your folks to detect potential threats
A big a part of your group is working remotely. Flexibility comes with an elevated charge of threat related to it. Distributors entry your system from places unknown and that will increase your possibilities of being uncovered to cyber assaults.
Conduct safety consciousness coaching packages and practice them on the group’s safety protocol with mock threats and stealth assessments. Implement periodic password adjustments and encourage them to make use of safe log-on processes.
Instill cybersecurity as a accountability fairly than an obligation.
Allow multi-factor authentication
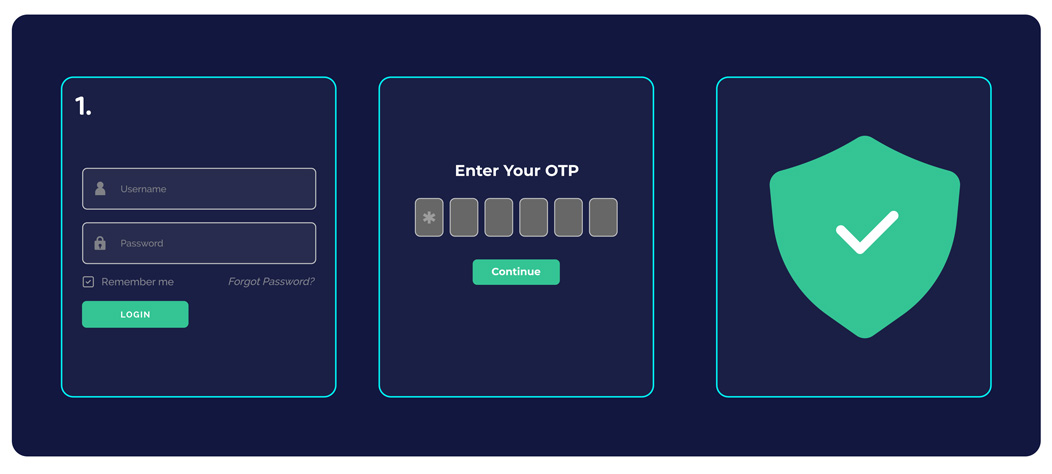
Multi-factor authentication is a foundational cyber protection mechanism in creating a powerful cyber safety plan. This enforces strict multi-layered authorization measures earlier than granting entry to methods or databases.
Multi-factor authentication must be applied throughout all methods, networks, and purposes throughout the group. Id and Entry Administration methods (IAMs) additionally act as an efficient method for directors to observe and establish suspicious on-line exercise in a cloud-based surroundings.
Carry out penetration assessments
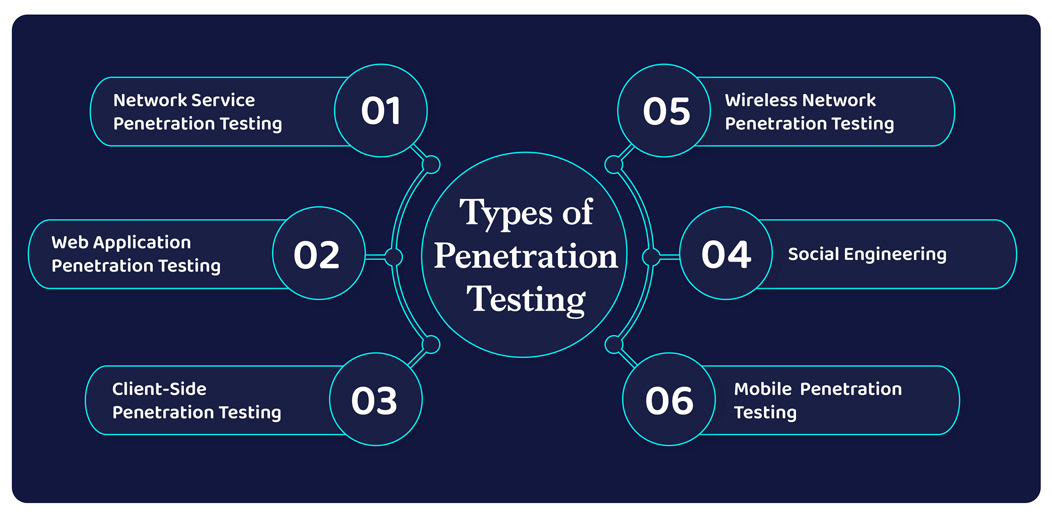
When cyber safety challenges are rising in quantity, dimension, and types, organizations are compelled to undertake a cybersecurity plan that helps defend themselves no matter their dimension. Penetration testing turns into an integral a part of a complete cybersecurity technique for the truth that it helps organizations detect loopholes of their present cybersecurity plan.
Throughout penetration testing, mock assaults are carried out to detect vulnerabilities brought on by {hardware} or software program design flaws, inefficient password administration, or compromises made by human intervention. Penetration testing must be carried out on all group networks, purposes, {hardware}, software program, and person conduct.
Risk intelligence assist corporations leverage the facility of information to make security-backed risk choices and construct efficient protection mechanisms. This predictive functionality helps establish attackers and reply sooner to risk incidents. Risk intelligence is delivered by way of implementing the precise instruments, strategies, and procedures (TTPs).
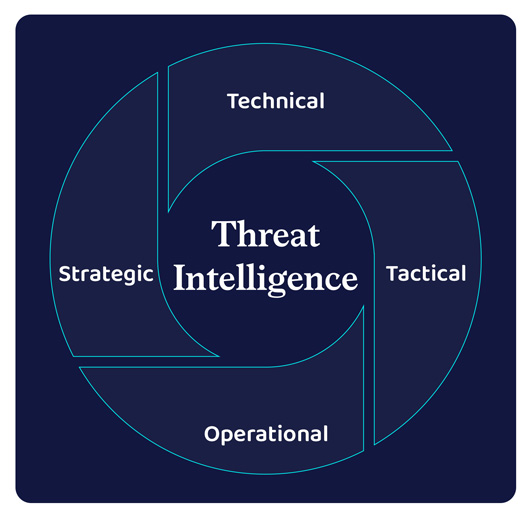
Risk intelligence is employed in 4 types—tactical, technical, strategic, and operational. Whereas tactical risk intelligence identifies easy indicators of compromises comparable to malicious IPs, URLs, or domains, technical risk intelligence devises a defensive mechanism based mostly on clues or proof derived from earlier assaults comparable to reported IP addresses, the content material of phishing emails, malware samples, and fraudulent URLs, to establish the opportunity of future assaults.
Each strategic and operational risk intelligence wants human intervention to be totally succesful. Strategic risk intelligence delivers insights into the threats, preventive measures, and severity of the threats to the group’s cybersecurity workforce. Operational intelligence analyzes the who, why, and the way of assaults and supplies organizations with a sensible view of potential assaults.
Create a cell incident response plan
Typically neglected, cell units additionally pose critical safety points for a company. Cell units are extra prone to information breaches and cyber threats. Therefore together with them within the cybersecurity structure is of prime significance.
Corporations should create an actionable incident response plan to safeguard the system earlier than exploitation. As a primary step to drafting an incident response plan, organizations should define the scope of incidents and methods to detect and comprise threats. A compact incident response plan should additionally define strategies to eradicate dangers, restore methods, and continuously monitor to mitigate dangers.
Client Sentinel Community, an investigative cyber device by FTC, analyzed over 5.7 million experiences within the 12 months 2021 out of which 49% had been fraud and 25% constituted identification theft. Whereas each circumstances are critical causes for concern most corporations again out contemplating the fee concerned in implementing a powerful cybersecurity structure. If that’s in your thoughts then what you need to know is {that a} single assault of any form, be it an information breach, malware, ransomware, or DDoS assault, prices corporations of all sizes a mean of $200,000, and plenty of affected corporations exit of enterprise inside six months of the assault, in keeping with insurance coverage firm Hiscox.
So, what’s your cybersecurity plan?
